
Saturar prosperidad Inspector cyber attack map Paloma Un fiel
This organizational structure, combined with deep pockets resulting from past exploits or nation-state sponsors, facilitates their offensive stance, allowing them to experiment with and incorporate game-changing technologies, such as new generative AI, that make their attacks more complex and harder to detect.

Real Time Cyber Threat Maps YouTube
Cybersecurity Event/Threatgroup Trackers. The CyberWar Map and Other Cybersecurity Trackers. , Digital and Cyberspace Policy Program, Council on Foreign Relations. APT Groups and Operations spreadsheet. , Center for Strategic and International Studies (CSIS) Targeted Cyberattacks Logbook.
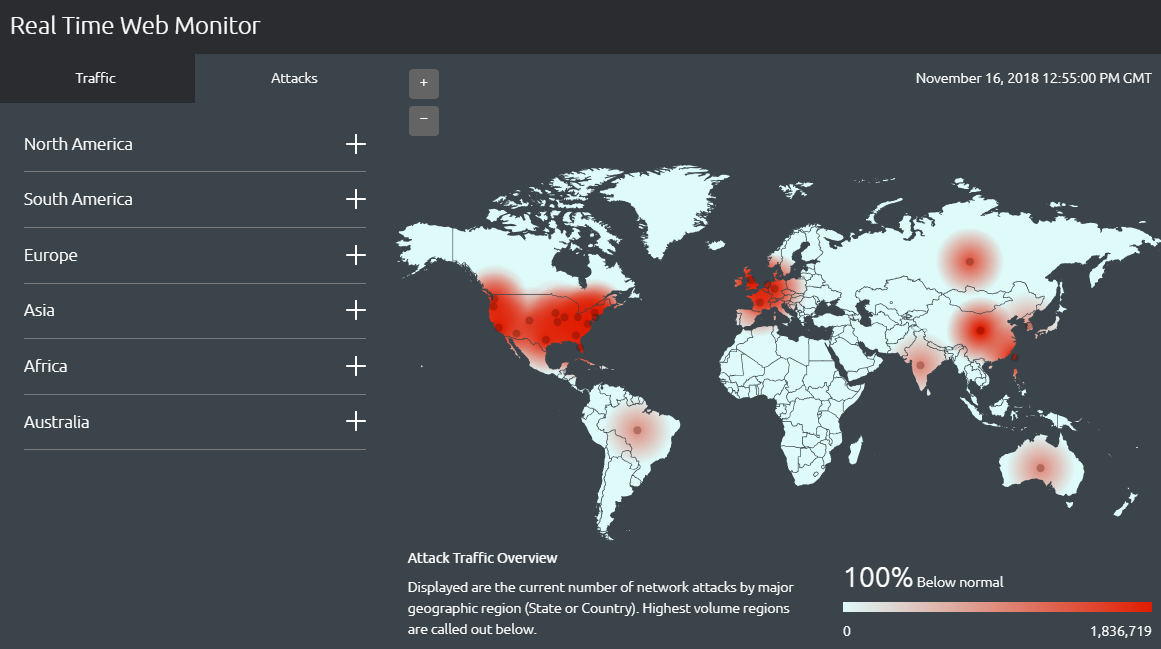
Top Ten Hacking Attack Maps and How They Can Help You
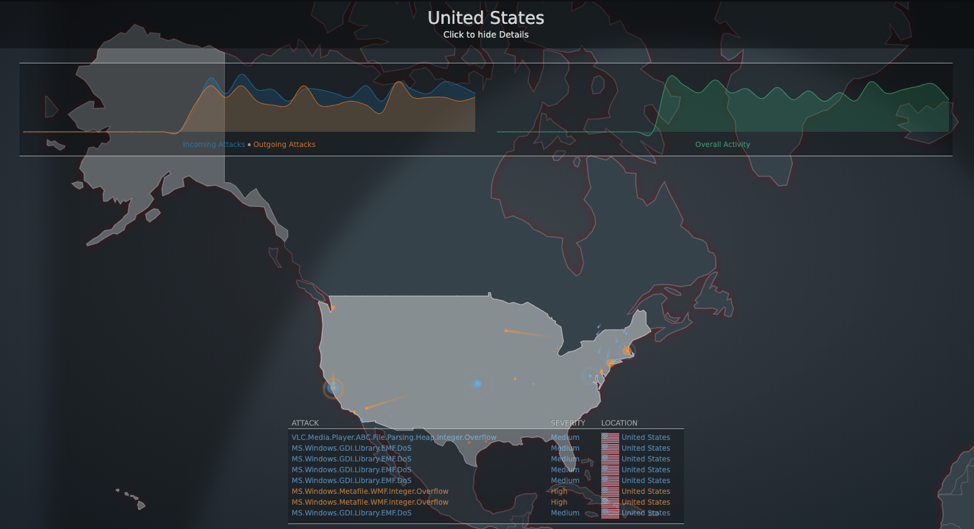
5.2.0. Attack Map. Attack Map is a visual representation of the entire network showing real endpoints, Decoy VMs, and ongoing attacks. The nodes on the map are color-coded by severity. , and Gateway. Click to view the attack history including AttackerStart TimeIncident ID.

RealTime Threat Maps ControlTrends
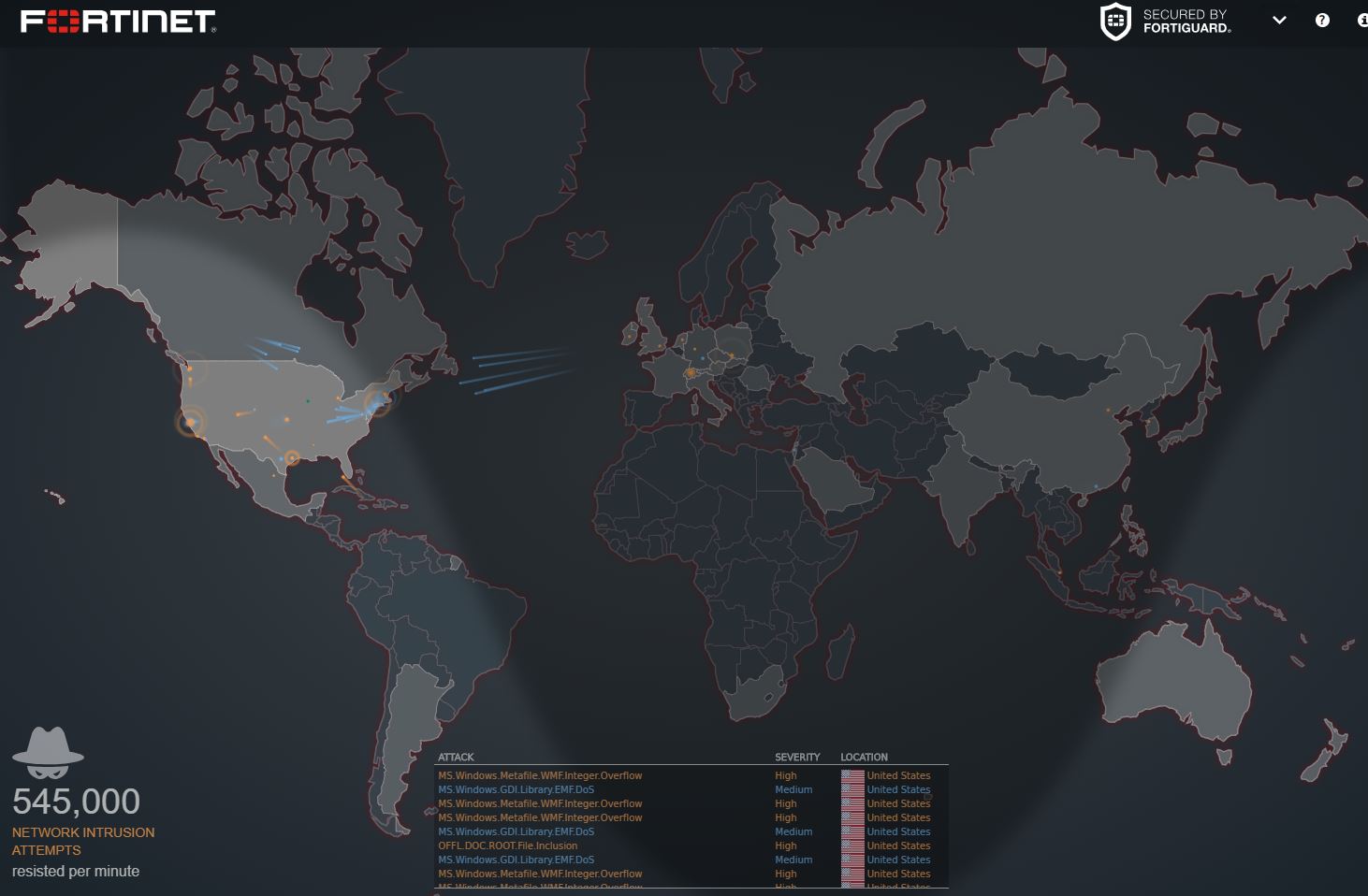
To help you and your business feel confident in your ability to protect yourself against the threats that continue to come our way, this report looks back on the cyber threat landscape of the first half of 2022 using our global array of sensors monitored by FortiGuard Labs. Here's what we learned: Ransomware Roundup:

globální podvod paprsek cyber threat map Usnadnit ret budoucnost
7 live cyber attack threat maps in 2020 1. Our favorite real-time worldwide cyber attack map is from Kaspersky Lab. It looks incredibly sleek. In fact, it can easily be a conversation starter at your next party because it also works great on phones.
The Ultimate Guide to Cyber Threat Maps CISO Global (formerly Alpine
March 25, 2022 1:00 pm MT. MITRE Engenuity's Center for Threat Informed Defense partnered with several security vendors and alliances to create a data format describing adversary behavior.

Live Threat Map YouTube
What are cyber attack threat maps? How do cyber Attacks work? 10 Cyber Attack Maps 1.Kaspersky Cyber Attack Map 2. Norse Attack Map 3. Arbor Networks 4. Digital Attack Map 5.Akamai

5 best malware tracker maps to see security attacks happen in realtime
Threat Map is a feature of FortiADC that allows you to visualize the network attacks detected by FortiGuard Labs across the globe. You can filter the map by time range, attack type, severity, and source or destination country. Learn how to configure and use Threat Map to monitor and protect your network.
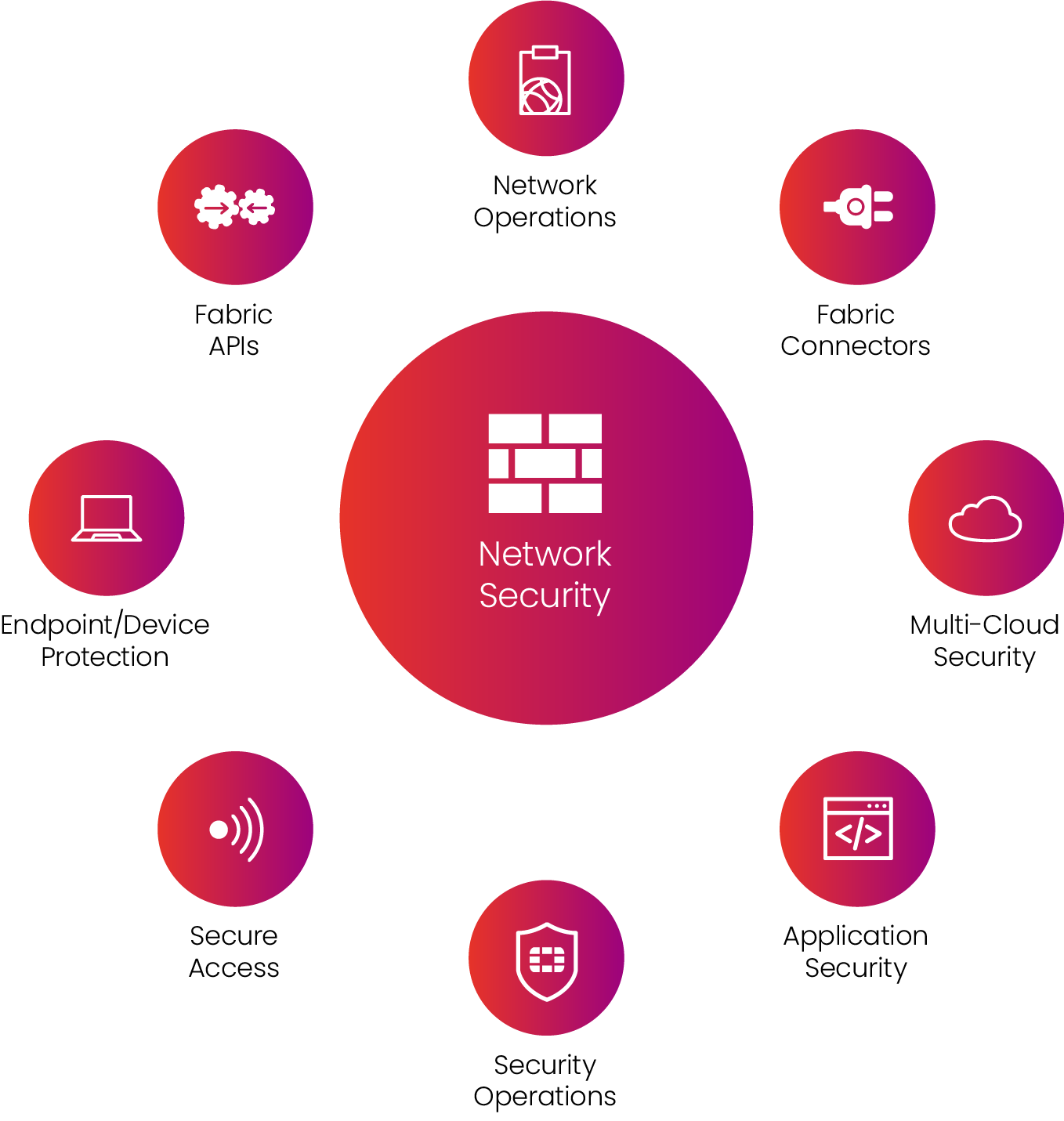
Security Fabric Solutions Exclusive Networks Austria
Fortinet's cyber attack map looks similar to the one from Norse and appears to show a playback of recorded events. As the attacks are displayed, a rotating breakdown of various stats.

Live cyber attack map FlowingData
Fortinet Threat Map The Fortinet Threat Map provides live updates on threats such as malware, botnets, and DDoS attacks. Utilizing its extensive global threat intelligence network,.
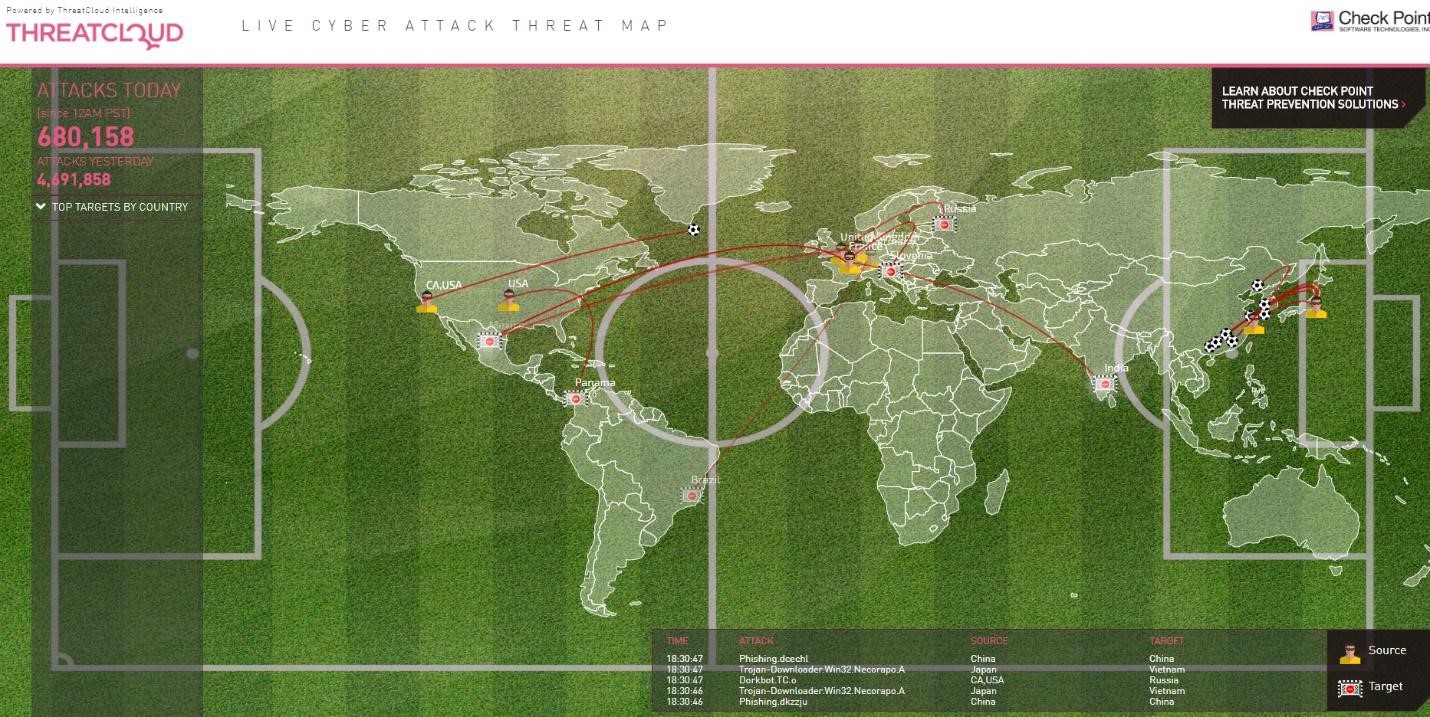
Track Cyber Attacks Happening All Over The World Using These Maps
FortiGuard Labs is Fortinet's in-house security research and response team, with over 10 years of proven threat prevention leadership, specializing in developing new adaptive defense tools to help protect against multi-vector zero day attacks. This global team oversees all of Fortinet's security services, delivering real-time, comprehensive.

Top 7 Cyber Attack Maps Hacking News
A Fortinet Cyber Threat Assessment can help you better understand: Security Risk - which application vulnerabilities are being used to attack your network, which malware/botnets were detected, what phishing attacks are making it through your defenses and which devices are "at risk"— for security breach probability.

Relatório de Ameaças Virtuais Nenhuma Empresa Está 100
A cyber threat map, also known as a cyber attack map, is a real-time map of the computer security attacks that are going on at any given time. One of the most famous was released by the company Norse and went so viral, even among non-hackers, that it got its own story in Newsweek in 2015. The map itself looks like a global game of laser tag.

Top 15 Live Cyber Attack Maps for Visualizing Digital Threat Incidents
Is your network security keeping up with the latest threats? Request a free threat assessment today and find out about your vulnerabilities, user productivity, and network performance. ATTACK LOCATION SEVERITY Click for Details Incoming Attacks Outgoing Attacks Overall Activity Enlaces rápidos
Top 8 Cyber Threat Maps To Track Cyber Attacks
The Cybercrime Atlas initiative is about driving real impact and is a coordinated effort to create a chain of disruption in the world of cybercrime. We are excited to continue our work with private and public sector leaders to help make our digital world a safer place." News Summary

download geraseek
Is your network security keeping up with the latest threats? Request a free threat assessment today and find out about your vulnerabilities, user productivity, and network performance. ATTACK LOCATION SEVERITY Click for Details Incoming Attacks Outgoing Attacks Overall Activity Quick Links